[Blog post]
Digital healthcare: Security vs usability?
A decision between security & usability? How the factors security and usability influence each other in digital healthcare.
10. January 2023
The digitization of healthcare is an indispensable step in meeting current challenges such as staff shortages, cost pressures and sustainability. Digitally mapped processes and data offer scope for new diagnostic and treatment options in the context of personalized medicine and also facilitate communication between internal and external players within the healthcare system. Individual patients themselves are also given greater influence to manage their own health through various apps and freely available information on the Internet._
The benefits of a modern, digital healthcare system are crucial and unthinkable, yet an advancing digitalization of processes and data also means at the same time that there is a larger attack surface for cyberattacks. This is especially critical in the context of highly sensitive data processed in healthcare. It is therefore clear that digitization must always go hand in hand with a strong cybersecurity strategy. As part of this, a wide variety of measures are taken, such as providing special training for employees, protecting everyday processes and applications with passwords and, in the best case, multi-factor authentication, and only granting access to authorized persons. In the already overburdened healthcare sector, which has to be able to act very quickly at decisive moments, these important and sensible measures often fail due to usability. This is because, as a rule, not only one login is required here, but several, time-consuming logins with a large number of applications and personnel with different authorization levels. But does good security always have to go hand in hand with poor usability? Or is there another way and how do the two factors influence each other?
The relevance of usability & security in the context of digital health products
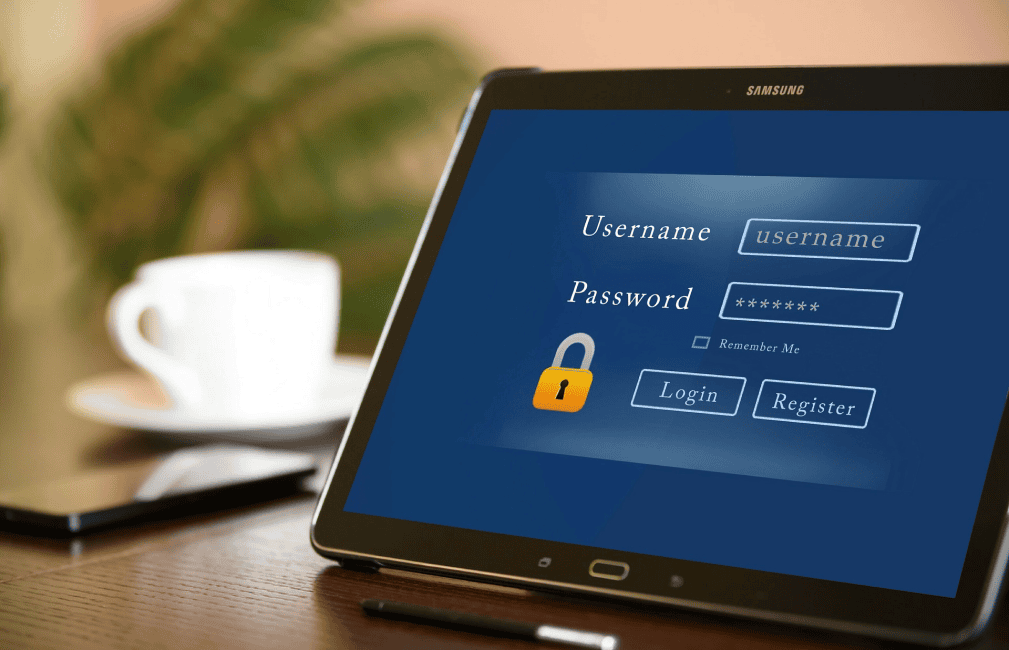
The first user experience with a digital application in the healthcare sector is often the registration and account setup process, as well as the subsequent login. If inadequate usability complicates the process, this negative user experience will result in a poorer overall impression of the product and prevent patients from using the health app willingly and conscientiously.
The same applies to the daily processes required in a professional context. For example, employees are given access with unique, secure passwords for each application to prevent unauthorized access to patient examination results that require protection. However, a variety of separate applications are used here, which require different passwords.
As a consequence of the poor user experience with a security feature that is difficult to understand or use, users are tempted to bypass these complicated steps. With multiple-use, simple passwords or shared access, they create a strong vulnerability in security. The effectiveness of a security measure therefore always depends on its usability: If it's not usable, it's not secure (Jared Spool). Conversely, this insight means that the two elements must be considered together from the outset. This process is referred to in practice as Security by Design, security aspects must be included in the development process from the beginning and all relevant stakeholders (IT, data protection, DevSecOps) must be involved throughout the course of the project.
The basic development process for a secure & user-friendly solution.
From a user experience (UX) design perspective, this process starts with the basics of good software design, which also applies to security measures:
- Availability: access is always available when needed.
- Robustness: use is possible without glitches, data loss, or transmission errors.
- Error tolerance: The ability to correct data in the event of erroneous input.
- Comprehensibility: clear, explanatory language of information and error messages.
- Accessibility: The accessibility for different target groups.
- Reliability: Consistency in user guidance in the form of platform-specific style guides.
- Confidentiality: The protection of confidential data from unauthorized access.
In addition, the level of security required should be defined in advance. Considerations here include when which level of authentication is required, which data is collected, how many backups are necessary, and where they are stored. In order to include all relevant factors in the design process, UX designers have various toolsets at their disposal, such as user journey mapping, personas and also antipersonas. With the help of an antipersona, for example, the threat situation can be assessed in advance and the necessary countermeasures prioritized. Wireframes and prototypes help to implement these as comprehensibly as possible.
Usable security for digital health applications in practice
In order to be classified as useful for both healthcare workers and patients for given standard topics such as documentation etc., the mentioned requirements have to be implemented. As a way to communicate this achieved level and to create trust, certifications are a possibility. In the healthcare sector, there are no uniform, industry-specific seals, such as Trusted Shops is for the e-commerce sector, for example, but there are standards such as the ISO standard for information security management, the IEC standard for usability for medical devices and, for example, the BfAM certifies apps if they meet the security requirements of the BSI. These include a protection needs analysis with regard to the basic values of information security such as confidentiality, integrity and availability, encryption of data, password specifications such as minimum length and misuse counters, two- or multi-factor authentication and administration or transparency about protected access.
These specifications regarding password and authentication guidelines as well as access restrictions are the same ones that are also specified as measures of the cybersecurity strategy in healthcare, as mentioned at the beginning. However, to circumvent the challenges described, such as complexity and lack of user-friendliness, the use of an identity and access management (IAM) solution helps. Here, features such as transparent user and access management and password policies with integrated multi-factor authentication are mapped in a solution and then implemented securely and user-friendly as a single sign-on (one-time logon) instead of complex multiple logons.
IAM solutions as the standard for a functioning digital healthcare system.
The relevance of such a solution can be optimally illustrated using the example of health insurance. Here, specialist staff and customers have to log on and authenticate themselves internally to several systems and externally to the customer platform. Using single sign-on, which only allows access for authorized persons defined in advance in the IAM, only one login with one password is required instead of 5 different passwords. The time savings are enormous and password policies can be used both to control the strength of the password and to avoid accounts being shared due to lack of access or time. With respect to customer logins, there is clear transparency over authentication and reporting data.
To increase security beyond password policies and regulated access, multi-factor authentication should be configurable for all employees via the IAM solution, if desired. Instead of just username and password, logins are secured with additional factors. How strong this factor should be depends on the selected procedure. It is advisable to use an IAM solution with various integrated MFA procedures, so the appropriate procedure, from one-time password (OTP) via e-mail, SMS, app to hardware security keys or biometric data such as FaceID or TouchID, can be selected even according to the necessary security level of the healthcare facility. But here, too, usability is a decisive factor, because only if the IAM solution can be reliably operated without errors by administrators can accesses for employees be quickly created or deleted and security procedures adapted.
The right IAM solution for healthcare: Bare.ID
In principle, there are various solutions on the market, from elaborate proprietary software to innovative cloud solutions. However, since in-house operation of a solution or even the use of an on-premise solution entails enormous expense for development, operation and maintenance and often fails in practice due to a lack of resources (capital & know-how), it is advisable to use a SaaS solution for the healthcare sector. Our cloud IAM solution Bare.ID enables access from anywhere, anytime, without the resource consuming factors described above. At its core, Bare.ID uses the well-known, established open source IAM framework Keycloak and has extended this with numerous features. Unlike other leading US IAM SaaS providers, the solution is hosted, operated and developed exclusively in and from Germany, is at all times governed exclusively by German law and thus implements digital sovereignty and also meets the highest compliance guidelines. Bare.ID can thus be deployed in a carefree and GDPR-compliant manner even in the highly regulated healthcare sector. Bare.ID solves the usability challenges with a user-friendly, easy-to-use interface that clearly displays all necessary features and makes them conveniently accessible. This allows secure access to be quickly assigned to each user of a system and password sharing to be avoided.
With the use of Bare.ID as an IAM solution and a user-friendly designed login interface, software applications for the healthcare sector can meet both security and usability factors.
Ähnliche Artikel
Password manager vs. single sign-on: finding the right solution
The advantages and disadvantages of the two tools in terms of secure login processes and user-friendliness.

Multi-use passwords as a risk factor
Password vulnerability: According to a survey, 64% of employees use their passwords more than once

People as a vulnerability: Why social engineering is so successful
The danger of social engineering - Why is this form of attack so successful and how can companies protect themselves?

Get in touch
Request a non-binding consultation now and discover how Bare.ID can be integrated into your IT environment.
Software comparison
Contractual & Compliance
About Bare.ID
Newsletter
Sign up for our newsletter to stay updated.
I agree to receive further information and news from Bare.ID. For more information, please see our Privacy Policy.
Bare.ID represents user-friendly Identity & Access Management in the cloud. With Bare.ID, digital business processes and applications can be connected to a local user directory, benefiting from centralized security and Single Sign-On. Whether On-Premise, Hybrid, or Cloud, Bare.ID offers a multitude of pre-configured integrations. 100% security, Made in Germany.
Bare.ID's offerings are exclusively intended for business customers in accordance with §14 BGB. All prices are to be understood as net prices, plus applicable VAT at the time of billing.
Bare.ID is a product and registered trademark of Bare.ID GmbH - an AOE Group company © 2025 - All rights reserved.